Warning of scam email / social engineering / “CEO fraud” [15.02.2022, CISO] Broad-based campaign against TU employees - target presumably : money in the form of vouchers
The wave of fraud emails to employees of the TU Braunschweig reported on 14.1.2022 does not stop. The emails always seem to come from the respective management, matching the target group, whereby a different real sender is used for each organisational unit, typically a GMail account.
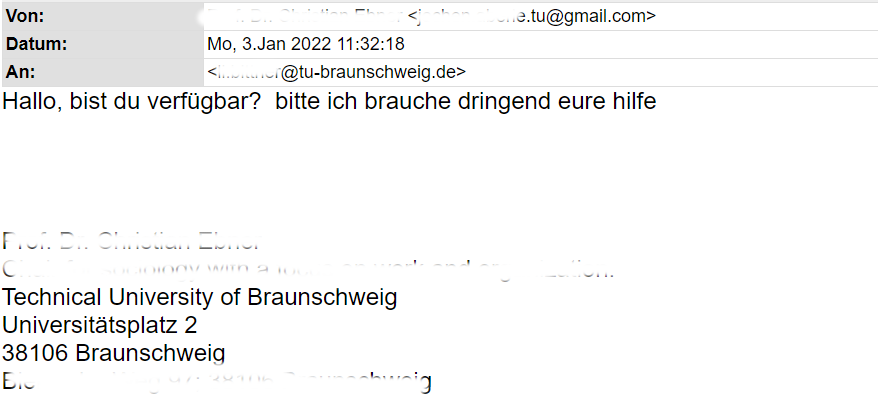
The mails supposedly come from the direct superior and (only) request immediate feedback (“Hello, are you available? please I need your help urgently”).
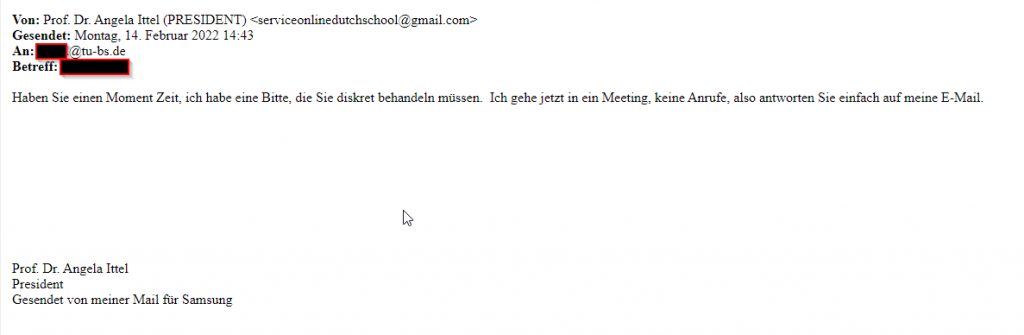
Since yesterday 14.2.2022, we have also been observing mails with the name of the receiving person as the subject and the sender
Prof. Dr. Angela Ittel (PRESIDENT) <serviceonlinedutchschool@gmail.com>
A fake email signature of the supervisor(s) is used. The mails always come from GoogleMail. The sender is also sometimes patterned after “real name of supervisor(s)” <Buchstabe.Nachnahme.tu@gmail.com>.
Here is an example:
As soon as someone replies to this mail, the scammers try to persuade the victim to buy voucher codes in a shop and transmit the codes to the scammers.
There have already been cases at TU Braunschweig where this was successful – the financial damage cannot/must not be compensated by TU.
Technically, the mails do not pose any danger: they do not contain any links or attachments. As they only contain one sentence each, automatic recognition and filtering is almost impossible.
Please do not reply to these mails under any circumstances!
Here is another example: